FortiGate
SecTrail CM enables automatic deployment and renewal of SSL certificates by establishing agentless connections to FortiGate firewall devices.
Connection Requirements
| Requirement | Detail | Description |
|---|---|---|
| Protocol | REST API (HTTPS) | FortiGate's native REST API is used |
| Port | 443 | Standard HTTPS port or custom management port |
| Authentication | Username and Password | Authentication via Username and Password |
| User Permission | Admin or Certificate Manager role | Certificate upload and configuration permission |
Automated Operations
SecTrail CM automatically performs the following operations on FortiGate:
- Certificate and Key Upload: Secure transfer of SSL certificate and private key to the device
- SSL Profile Update: Updating SSL inspection profiles
- Policy Update: Updating firewall policies to use the new profile
- Configuration Commit: Making configuration persistent
Configuration Steps
1. Creating FortiGate User
Navigate to Automation > Device Users and create a user for FortiGate.
2. Adding FortiGate Device to SecTrail CM
Click Automation > Devices > Add New Device button and enter the following information:
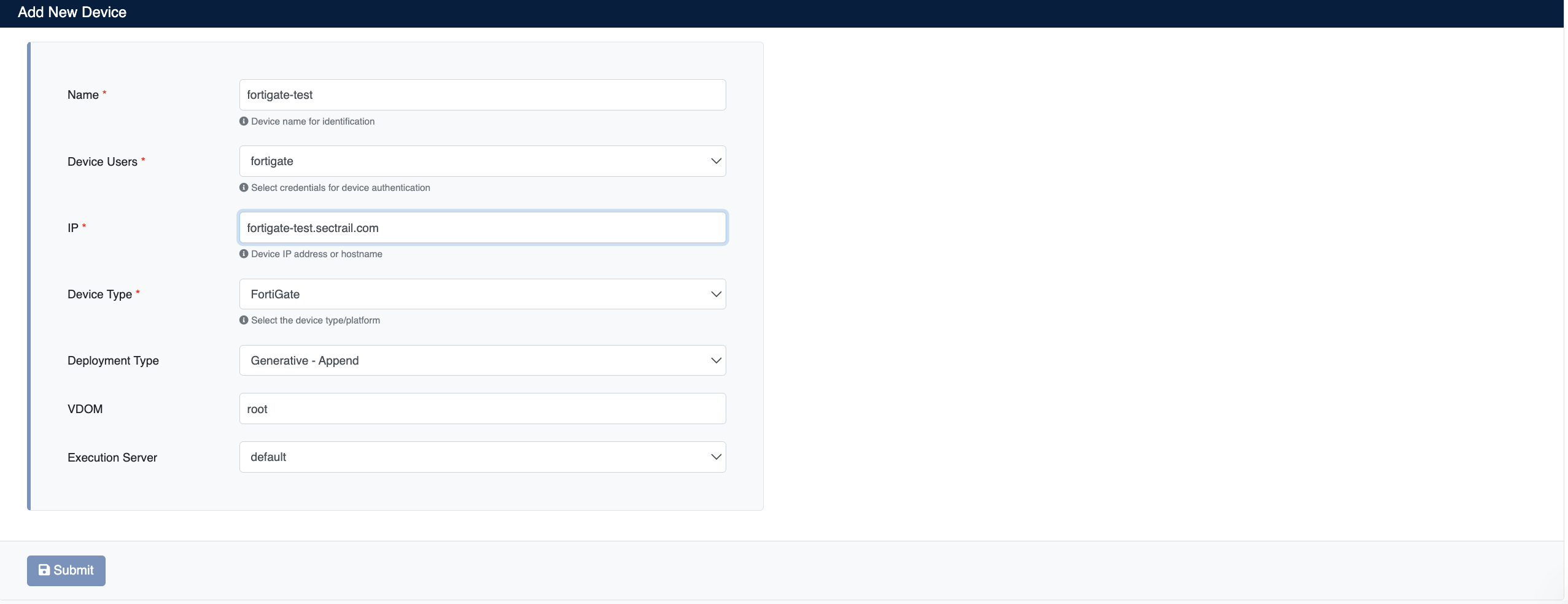
- Name: Provide a descriptive name for the device
- Device Users: Select the user created in Step 1
- IP: Enter the FortiGate device IP address or hostname
- Device Type: Select
FortiGatefrom the dropdown menu - Deployment Type: Select deployment type
- Generative - Append: Creates a new SSL profile, adds the new certificate to it, and associates it with matching policies
- Generative - Replace: Creates a new SSL profile, replaces the certificate within it, and associates it with matching policies
- Override - Append: Adds the new certificate to the existing SSL profile
- Override - Replace: Removes the current certificate from the existing SSL profile and adds the new one
- VDOM: FortiGate VDOM name (e.g.
root) - Execution Server: Server to use for executing deployment operations
After the FortiGate device is added to SecTrail CM, all certificates defined on the device are automatically included in the discovery period and scanned regularly. Automatic alarms are created for certificates that are about to expire or have issues.
3. Viewing Device Information
After the device is added, it will be displayed in the Automation > Devices list. Click on the row to view device details:
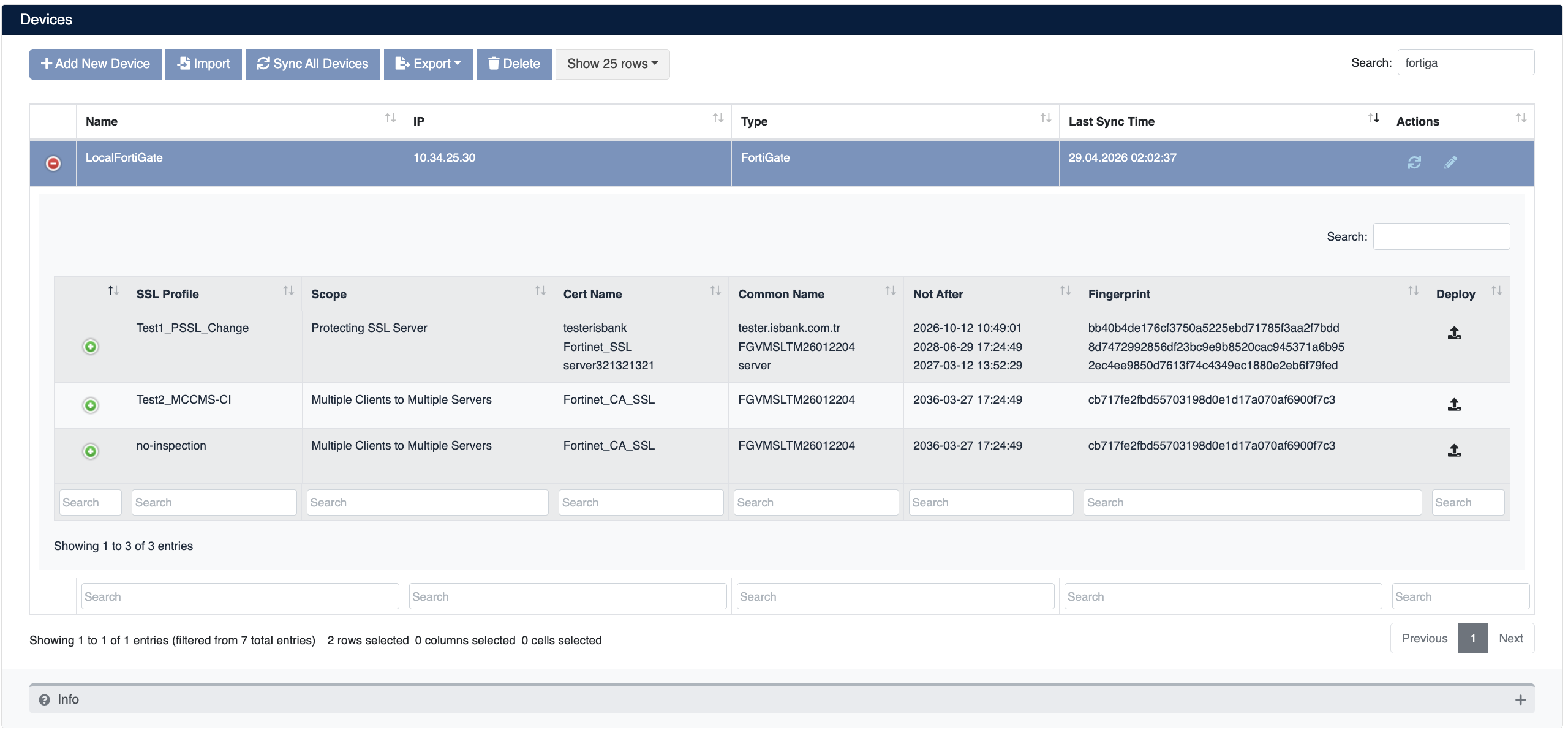
- SSL Profile: SSL inspection profile name associated with the certificate
- Scope: Scope of the SSL profile (e.g. Protecting SSL Server, Multiple Clients to Multiple Servers)
- Cert Name: Name of the certificate defined on the device
- Common Name: Common Name (CN) information of the certificate
- Not After: Certificate expiration date
- Fingerprint: Certificate fingerprint
- Deploy: For certificate deployment
Certificate Deployment
Step 1: SSL Profile and Certificate Selection
- Select your FortiGate device from Automation > Devices
- In the device details, find the SSL profile where you want to deploy the certificate
- Click the Deploy button on the relevant row
- In the Deploy Certificate window that opens:
- Virtual Servers: Target virtual server information is displayed (SSL Profile / Common Name / Installation Target / Not After format)
- Deploy Type: Displays the configured deployment type (e.g. Generative-Replace)
- Replace Certificate: Select the existing certificate on the device to be replaced
- Certificate: Select the new certificate to deploy from the dropdown menu
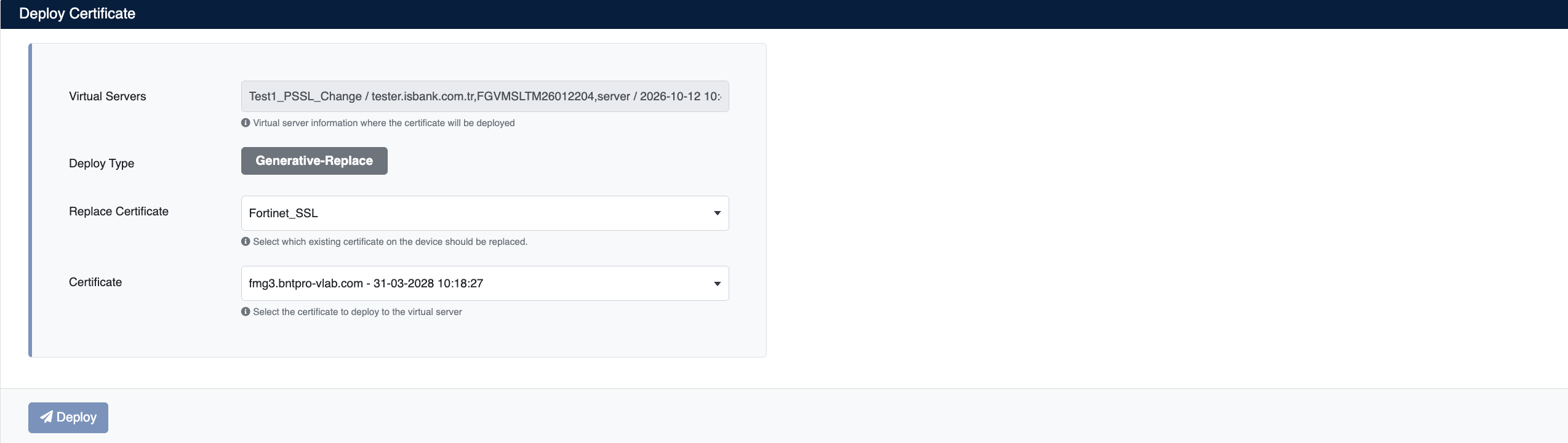
Step 2: Starting the Deployment Process
Click the Deploy button to start the certificate deployment process.
Step 3: Process Tracking
The deployment process can be tracked from Automation > Processes:
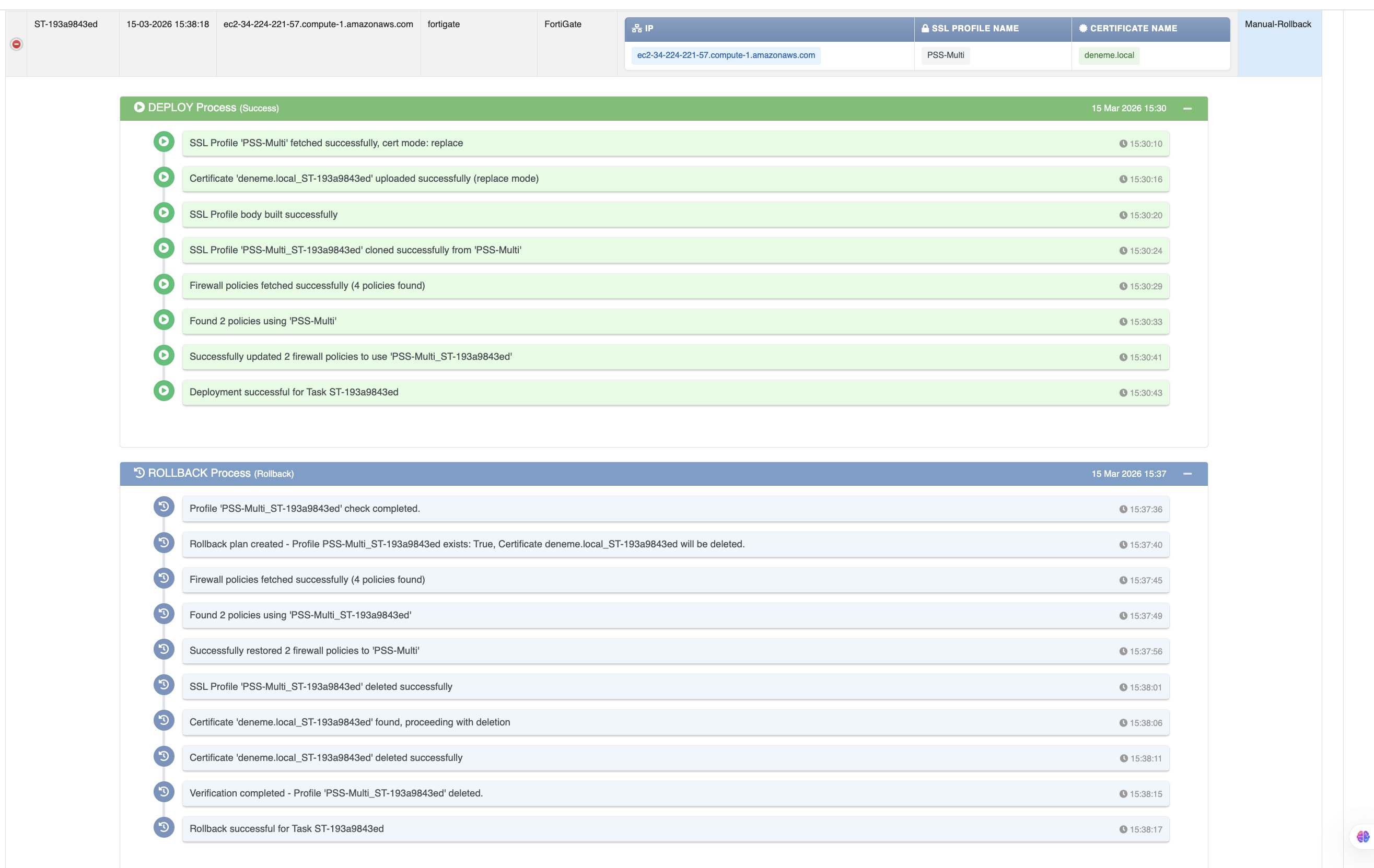
Operation Details
The following steps are performed during deployment:
| Step | Operation Description |
|---|---|
| 1 | SSL profile is fetched and cert mode is determined |
| 2 | Certificate is uploaded to the device |
| 3 | SSL profile body is built |
| 4 | SSL profile is stored successfully |
| 5 | Firewall policies are fetched |
| 6 | Matching policies are updated to use the new profile |
| 7 | Deployment completed successfully |
Rollback Operation
The Manual Rollback feature can be used in case of issues after certificate deployment.
If an error occurs at any step during the deployment process, the system automatically performs a rollback and all changes are reverted.
Rollback Steps
- Navigate to Automation > Processes
- Find the operation you want to rollback
- Use the Manual-Rollback option in the Status column
- Confirm
Operations During Rollback
| Step | Operation |
|---|---|
| 1 | Rollback plan is created and certificate to be deleted is identified |
| 2 | Firewall policies are fetched |
| 3 | Matching policies are reverted to the previous profile |
| 4 | New SSL profile is deleted |
| 5 | Certificate is deleted from the device |
| 6 | Rollback completed successfully |