Account Security Without Access Control Is an Illusion
One morning, you arrive at work and see that all security systems are running smoothly. The firewall is active, the antivirus software is up to date, and the VPN is on. Everything appears to be in order. Yet on that same day, an account belonging to a former employee who left your company two years ago is still active, and someone has used that account to access customer data.
This is not a fictional scenario. A large portion of corporate security breaches originate not from external attacks, but from internal threats. And these threats almost always have one thing in common: inadequate access control.
“Internal threats” do not refer only to malicious employees. Forgotten accounts, excessive privileges, and unmonitored access create the same opening.
What Is Access Control and Why Is It Critical?
Access control is the security mechanism that determines who can access which system, when, and with what level of authorization. It sounds simple, doesn’t it? But in practice, many organizations have serious gaps in this area.
When an employee joins the company, they are granted access to the systems they need. Over time, however, these permissions expand due to new projects, temporary responsibilities, and urgent situations. In most cases, temporary privileges become permanent. No one thinks to revoke them. As a result, an employee in the accounting department may eventually end up with access to HR systems, customer databases, and even server management panels.
In cybersecurity, this is called privilege creep. And it progresses silently.
The Biggest Enemy of Account Security: Over-Authorization
Many IT managers evaluate account security solely through strong password policies and authentication layers. Yet for an account to be truly secure, it is not enough that only the right person can log in. That account must also have access only to the right resources.
Consider this: a malicious actor compromises an employee’s account. If that account’s access is limited strictly to the employee’s area of responsibility, the damage remains minimal. But if the account has broad access across the system, a single set of credentials can open the door to the entire organization.
Strong authentication + weak access control = incomplete security.
That is why access control is not merely a complement to authentication; it is a prerequisite for it. Verifying who the user is is critical, but determining what that user can access is just as important.
The Three Faces of Insider Threats
Insider threats do not fit into a single mold. They appear in three different forms:
- Malicious Insider Threat: An employee deliberately leaks data or damages the system. This is actually the least common type, although it attracts the most attention.
- Negligent Insider Threat: An employee unintentionally creates a security vulnerability. Clicking on a phishing email, using a weak password, or accessing the system from an unauthorized device all fall into this category. According to statistics, the vast majority of insider-related breaches belong to this group.
- Compromised Account Threat: An external attacker obtains the credentials of an internal user and logs into the system as if they were a legitimate employee. Although this threat originates externally, from an access control perspective it behaves entirely like an insider threat.
The common solution to all three scenarios is the same: knowing who the user is is not enough; what they are allowed to do must also be controlled.
The Principle of Least Privilege: The Foundation of Access Control
In cybersecurity, the principle of least privilege states that every user should have only the minimum level of access necessary to perform their job. It sounds straightforward, yet in practice it is a principle many organizations ignore.
There are several reasons for this. First, granting access is easy; revoking it is inconvenient. Second, in urgent situations, security is often sacrificed for speed, and temporary exceptions become permanent. Third, access control requires regular reviews, and those reviews are frequently neglected.
Organizations that fail to review access permissions every six months are unknowingly accumulating security gaps.
To implement the principle of least privilege, the first step is to gain a clear picture of the current state: Who can access what? Is that access still necessary? Have the accounts of former employees been disabled? The answers to these questions often surprise IT managers.
Authentication Alone Is Not Enough
Multi-factor authentication provides a critical layer of account security. Even if a password is stolen, the attacker cannot access the system without a second verification factor. This is an extremely effective defense against external attacks.
However, authentication cannot replace access control. Once a user successfully verifies their identity, what they are able to do depends entirely on access policies. Letting the right person into the system is only the beginning of security; limiting that person’s movements within the system is the real safeguard.
When these two layers work together, true defense in depth is achieved. Authentication opens the door; access control determines which rooms you are allowed to enter.
Practical Access Control Steps for IT Managers
Implement role-based access control (RBAC): Define permissions by roles instead of by individual users. This way, when a new employee joins, assigning them to the appropriate role is enough instead of granting permissions one by one.
Conduct regular access reviews: Review all user permissions at least once every six months. Departed employees, role changes, and temporary privileges must all be checked during these reviews.
Isolate privileged accounts: Administrative accounts should not be used for routine daily tasks. Access to critical systems should be granted only when necessary and always under monitoring.
Automate offboarding processes: When employees leave the company, account deactivation should not depend on a manual reminder. The process should be automatic and auditable.
Monitor access logs: Who accessed which system, and when? Unusual access patterns are often the earliest signs of major breaches. That is why log management and monitoring are critically important.
Conclusion: Security Starts From Within
In cybersecurity, we often focus on external threats. We strengthen firewalls and take precautions against outside attacks. Yet the most serious risks are often already inside: in forgotten accounts, excessive privileges, and unmonitored access.
Access control is the primary way to prevent these risks. Verifying a user’s identity is important, but controlling what that user can do is equally part of the IT manager’s responsibility. When authentication and access control work together, account security becomes truly effective.
As you strengthen your defenses against outside threats, do not overlook what is happening inside. The biggest vulnerability often comes from the most familiar place.
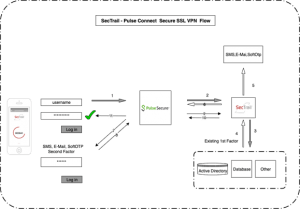
If you want to manage authentication and access control under a single framework in your organization, SecTrail MFA offers a local multi-factor authentication solution that can integrate with your existing infrastructure. With support for Active Directory, RADIUS, and SAML 2.0, it is designed to work seamlessly with enterprise systems. Contact us to learn more about the platform.